The Future of Mac Device Management with macOS Catalina 10.15
 Kandji Team
Kandji Team
Apple for business is growing. Modern businesses are choosing to run on Apple, and they are redefining how work gets done on iPhone, iPad, and Mac.
For Mac specifically, there are many things we are excited about in this release of macOS Catalina 10.15. We’ve noticed a thoughtful commitment to macOS in the workplace by ongoing support of the MDM ecosystem, investment in growing the MDM protocol, identity and SSO innovation, and nods to BYOD. The common thread through many of the changes was a balance of values between security and manageability, woven together to create a delightful user experience.
We’ve spent the last few months in the weeds with the new device management documentation and beta software (and the last decade living and breathing Apple device management). This post will explore what’s new in 10.15, why it is a testament to the growth of Apple for business, and specific ways that Kandji is fully supporting it.
We’re ready, are you?
Before we dive into the details of how device management will look different with macOS Catalina 10.15, we want to confirm that Kandji supports macOS Catalina from day zero.
All new functionality within Kandji has been fully tested within the beta program, so you don’t have to worry about any friction during your OS update.
However, as a general best practice, we recommend taking some time to thoroughly test in your own environment and letting Apple come out with its first “point” update (in this case, macOS 10.15.1) before rolling out the new macOS to your organization. After that, you can roll out the update smoothly to take advantage of the new security enhancements (we dive into detail on these below) and allow your users to access practical new features.
What’s new in macOS Catalina 10.15
The list of specific changes within macOS Catalina 10.15 is long, so we will only highlight here the ones we find most critical for an IT admin managing Apple devices to understand and prepare for. For the comprehensive list, refer to Apple’s developer resources and support site.
Security
The common theme we observed in the many security enhancements provided through macOS Catalina 10.15 is that the goal is to strike a balance between manageability and user productivity. We also noticed a strong support of the MDM ecosystem through enhancements like Enrollment Customization and mandatory device enrollment with Apple Business Manager, which will empower IT professionals to ensure every single device is managed and protected.
- Activation Lock: Activation Lock is now supported on all Mac devices running a T2 chip. Activation Lock was previously available only on iPhones and iPads but is now coming to Mac with Catalina. This update promotes both device security and user control, as it ensures the only person who can activate or erase a lost device is the user. MDM providers will be able to escrow bypass codes and have full control over devices that are locked by the Find My app.
- Notarization Required: Gatekeeper now requires notarization for all apps installed on Catalina, and will also check for known security issues before being allowed to run for the first time (and at periodic cadences afterward). However, if you have internal apps that are not notarized, you have the ability to allow them (see Application Allowing below).
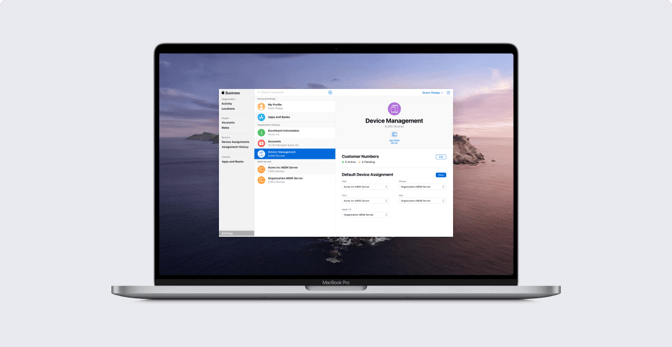
- Enrollment Customization: When using Apple Business Manager and a third-party MDM like Kandji, Apple is now allowing IT to provide custom branding, consent text, and modern authentication to their teams during enrollment. Learn more about what's new in our guide to identity and SSO.
- Device Enrollment Mandatory: If you’re using Apple’s Device Enrollment with Apple Business Manager, devices will automatically be supervised and enrollment will be mandatory. This enforcement was talked about in 2018, and Apple has followed through this year.
- DriverKit and User Space System Extensions: As kernel extensions (KEXTS) are being slowly phased out, Apple has increased the amount of DriverKit space, so that these programs can now run separately from the OS. This is enabled by a new filesystem architecture that separates OS and user data to ensure external data doesn’t interfere with the OS.
- Users Approve Kernel Extensions: You want to make sure kernel extensions are compatible with macOS 10.15 and allowed using a configuration profile. Newly loaded kernel extensions will prompt a user to restart before they are loaded by macOS.
- Find My Mac is Available Offline: As an extra security feature, if a device is lost or stolen, Apple has enabled a Bluetooth beacon from other Apple devices to locate a device, even if it is offline. Everything is encrypted, so no one’s privacy is breached during the process.
Managed Apple IDs and BYOD
- Managed Apple IDs: Apple is now allowing Managed Apple IDs to be created and assigned from Apple Business Manager, either manually or from Azure Active Directory. Whereas previously, Managed Apple IDs were typically used only for Apple Business Manager admins or managers, Managed Apple IDs can now be assigned to each user during enrollment. This means that employees can log into a Managed Apple ID on a work device, and IT can now send App and Book licenses (formerly VPP) to a Managed Apple ID for each employee instead of having to send it to their personal Apple ID. For more information, read our guide to Managed Apple IDs for business.
- User Enrollment: A new type of enrollment was released, called User Enrollment, that represents a significant step forward in terms of supporting BYOD use cases in the workplace while protecting user privacy. It essentially creates a partition between personal and work data, and limits IT’s control and visibility of personal data on User Enrolled devices. In the words of Todd Fernandez at the WWDC session What’s New in Managing Devices, “This is not a multi-user system. It's a multi-persona system. It's the same user wearing different hats.” Read our Apple IT guide to device enrollment to learn more about how this new type of enrollment fits in.
- Data Separation: When a device goes through User Enrollment, a separate Apple File System (APFS) volume is created. All business data is stored and encrypted on this APFS volume. When a device is unenrolled, all the data (apps, configurations, tracking, etc.) is automatically removed and destroyed, along with the cryptographic keys. The entire work identity disappears, and only the personal identity is left.
- Curated Management: Along with separating data, IT is limited from any invasive activities on that device after it is deployed through User Enrollment. For example, IT will not be able to wipe a user’s personal device, as there is no longer support for commands EraseDevice, ActiveSync, or RemoteWipe. IT also doesn’t have access to any personal data, including viewing which personal apps are installed. IT can, however, install needed workplace apps or take important security measures such as requiring a 6-digit passcode.
MDM Protocol
- New Payloads: The ever-expanding MDM protocol continues to grow, which increases the range of control that MDM providers like Kandji can extend to its IT customers. Examples include added support for the WPA3 security type to the Wi-Fi payload, and a new Certificate Transparency payload which allows organizations to opt-out sensitive domains. You can find the full list of new payloads in Apple’s developer documentation.
- Application Allowing: If you have internal apps that aren’t notarized, but that you want to keep using, you have the ability to allow them. MDM servers now have the ability to manage and escrow a bootstrap token to use with the Privacy Policy payload, which can now allow you to configure allowing, among other things like enabling keylogging or screen recording in the background.
Authentication
- Federating with Azure AD: Azure Active Directory (AD) now connects to Apple Business Manager. You can actually create Managed Apple IDs at scale during the enrollment process via the Azure AD integration. The Managed Apple IDs are created when users sign in with their business email. To learn more, read our guide to federated authentication, or our guide to using federated authentication to create Managed Apple IDs.
- Single Sign-On (SSO) Extension: Within macOS Catalina (as well as iOS 13 and iPadOS) Apple has launched a new SSO framework. Third-party vendors, such as Okta, can opt into this framework, and it is configurable within MDM solutions. To learn more about the new changes, read our complete guide for Apple IT on identity & SSO.
- Kerberos Extension: Building upon the SSO framework, Catalina also supports challenge-based authentication via challenge-based systems, such as Kerberos.
Other Foundational Changes
- Default Shell Changed from Bash to zsh: Bash is still available and supported, and your bash scripts will still run in bash, but zsh is now the default shell. To learn more about this change, read our guide to Mac scripting.
- Project Catalyst: Project Catalyst enables you to merge development for iOS and Mac apps. An iOS app can be run through a new Xcode development kit that can translate iPhone or iPad apps into Mac apps. This may have a big impact on how IT teams purchase and distribute Mac apps in the future. Today, many common business apps are not available in the Mac App store, such as Adobe Creative Cloud, Google Chrome, Zoom, and Sophos. If Project Catalyst enables more Mac apps to be available in the Mac App Store, that could simplify app management (for example, patching and auto-updating) for IT teams. Read our guide to app deployment for macOS to learn more.
- 32-bit Apps not Supported: 32-bit apps will not run on Catalina. Although they are becoming less common, 32-bit apps are less efficient than 64-bit apps. It’s worth taking stock of your application inventory and making sure you won’t run into any trouble with existing 32-bit apps.
Piloting an organization-wide OS update can be daunting — we know because we’ve been there. Before we were Kandji, we ran an Apple-certified IT firm that helped modern businesses manage Apple devices. From the strong knowledge base we gained, as well as experience deploying every other MDM solution on the market, we recognized a need for an Apple MDM solution that could accommodate growing businesses and increasing regulatory demands. With Kandji, we are ready to push macOS Catalina 10.15 to its limits in the workplace.