Introducing 120+ New Apple Device Restrictions
 Kandji Team
Kandji Team
Today, Kandji admins have 120 new one-click configurations at their fingertips. This new set of Apple device configurations is based on Apple’s Restrictions profile, which restricts the ability for users to take certain actions on devices such as accessing a specific app, service, or function.
Although the range of restrictions available is vast (for example, IT could do anything from deferring an OS software update to disallowing the use of Siri), the goal is to standardize device settings across your environment. This creates peace of mind for IT, and ultimately secures your devices to keep your data safe.
In this post, we’ll cover some background on Apple’s Restrictions profile, how to use it, and how Kandji’s unique implementation of this profile gives IT teams maximum flexibility by allowing you to create multiple Restrictions profiles.
Why the Restrictions profile matters
In our constantly evolving digital environment, security is not going to get any less important – but with tools like Kandji, it can get easier. That’s why Kandji is the only Apple mobile device management (MDM) solution with robust security and compliance tools built right in; it has features like 150+ pre-built parameters, one-click templates for common compliance frameworks such as the Center for Internet Security (CIS), and built-in remediation, even if your devices are offline. The introduction of this Restrictions profile to Kandji is significant because it gives our security-conscious user base more robust capabilities.
This release is also really important to the Kandji team because it shows our commitment to Apple’s MDM protocol. Apple continues to lead the charge in helping IT teams secure their environments while ensuring the best possible user experience, and we’re there every step of the way.
What is the Restrictions profile?
Apple’s MDM protocol contains sets of configuration profiles, and the Restrictions profile is one of them. These configuration profiles contain payloads, XML files (.mobileconfig files). An Apple MDM solution, like Kandji, can build device management functionality based on these profiles, allowing IT admins to securely and remotely manage Apple devices.
Apple’s Restrictions profile is just one of many Apple configuration profiles that Kandji supports, such as the Wi-Fi, VPN, and Privacy profiles – and many more.
What does the Restrictions profile do?
We won’t list every single one of the more than 120 restrictions available, but to provide an idea of the scope of this profile, here are a handful of common restrictions:
- Disallow changing account settings
- Requiring authentication before using AutoFill passwords
- Disallow modifying diagnostics settings
- Defer software updates
- Automatically reject untrusted HTTPS certificates
- Force encrypted backups
The Restrictions profile covers a broad range of actions within Kandji, organized into the following categories:
- Apps
- App Blocking & Allowing
- Autonomous Single App Mode
- Passcode & Authentication
- Lock Screen
- Accounts & Passwords
- Data Segregation
- iCloud
- Network
- Cellular
- AirDrop
- AirPlay
- AirPrint
- Apple Watch
- Diagnostics
- Files
- Find My
- Game Center
- Keyboard
- Media
- OS Updates
- Safari
- Siri
- OS & General
Enabling the Restrictions profile in Kandji
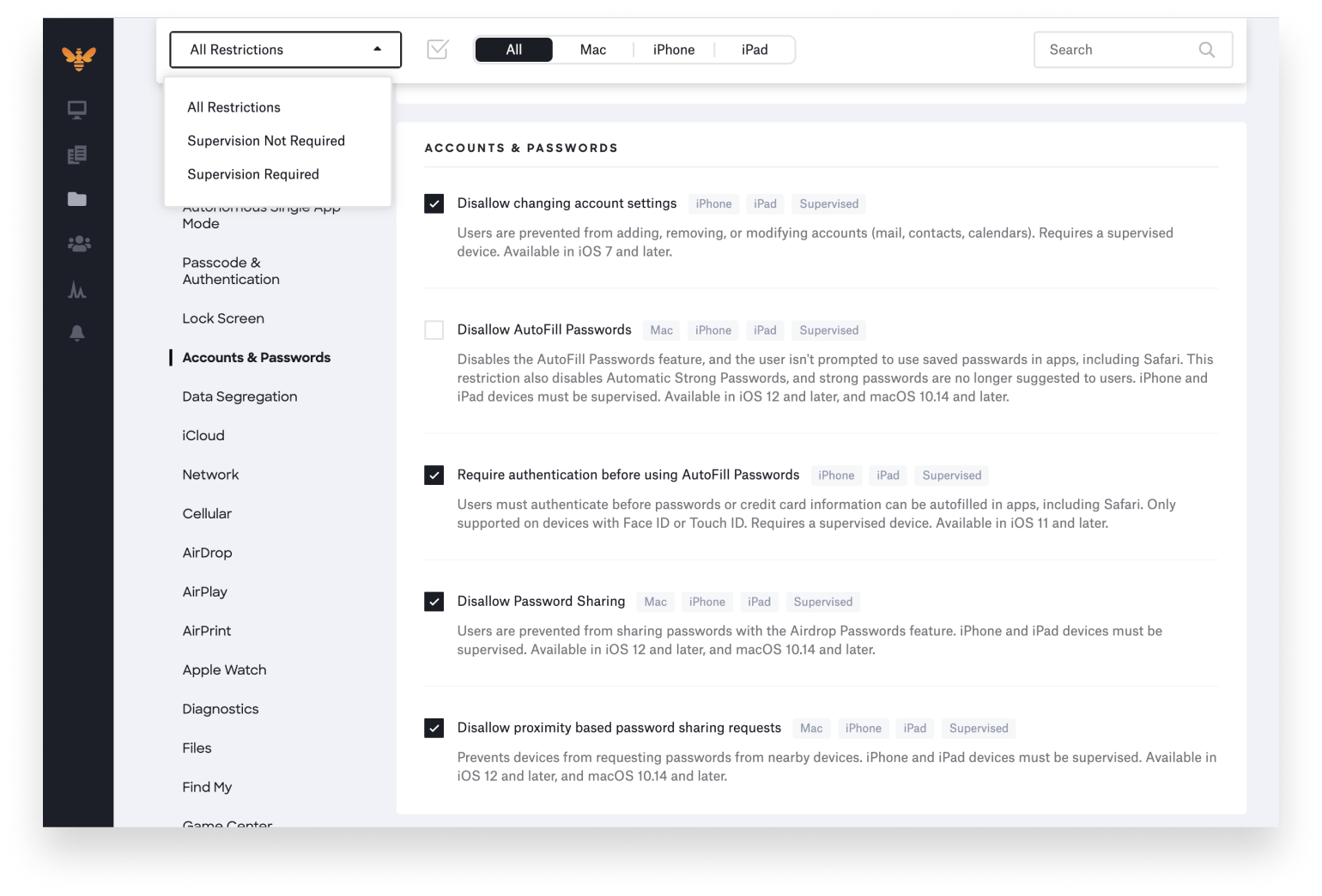
Our product team took both an elegant and practical approach to the implementation of this profile in order to give IT teams as much flexibility as possible. You can create multiple Restrictions profiles based on your needs; for example, maybe your sales team needs additional Media restrictions, or perhaps your executive team needs Cellular settings adjusted in a unique way.
Simply create a new Restrictions profile, turn on the restrictions you would like to enable, and then assign them to a group of devices using a Blueprint.
Here are some considerations when determining which restrictions to enable:
- OS Requirements: Minimum OS requirements are iOS 4.0+, iPadOS 13.0+, and macOS 10.7+.
- Device Types: You can filter between restrictions available for Mac, iPhone, or iPad.
- Supervision Required vs. Not Required: Some restrictions require Device Supervision, particularly the options for iPhone and iPad, but you can filter between supervision options according to your needs. To learn more about supervision and what it means, check out our Apple IT guide on device enrollment (UAMDM, TCC, and Device Supervision).
With innovation and iteration at the core of everything we do, we’re constantly building solutions to give you more of what you need and improve upon features you already love. With Kandji, you can be confident that your Apple fleet is in safe and secure hands from deployment to retirement.