How to Manage Activation Lock: A Guide for Apple Admins
 Mike Boylan
Mike Boylan
Activation Lock is a theft-deterrent feature found in iOS and iPadOS devices and modern Mac computers (with the Apple T2 Security chip and Apple silicon). When such a device is attempted to be set up after having been erased, it checks with Apple servers to see if Activation Lock is on. If it is, the device requires the user’s Apple Account password before it can be used again (reactivated). This effectively removes the device’s resale value, making it less attractive to thieves.
Given its dependence on users’ Apple IDs, Activation Lock might seem to be a bad fit in organizational settings with supervised devices. But it doesn’t have to be. You can still allow users to use Find My, and you can take advantage of Activation Lock’s theft deterrence without Apple IDs. In this post, we’ll go over what Activation Lock is, how it can be managed with MDM, and explore some common workflows as well as a few known gotchas.
What Is Activation Lock?
Activation Lock was first introduced in iOS 7 and came to Mac in macOS Catalina (for supported models). Setting aside any organizational considerations of the feature for now, it’s a server-side protection mechanism that locks an Apple device to a specific Apple ID when Find My is turned on. Though devices generally ‘know’ whether or not Activation Lock is turned on, the source of truth is always Apple’s servers.
Supported devices check in with Apple following an erase, and Apple’s servers either allow the device to proceed with activation or they don’t. If they don’t, in the case of iOS or iPadOS devices (as Apple Platform Security explains):
Devices that are Activation Locked prompt the user for the iCloud credentials of the user that enabled Activation Lock at this time.
In the case of Mac computers:
If the device is Activation Locked, recoveryOS prompts the user for iCloud credentials of the user that enabled Activation Lock...
In either case, the device is rendered unusable until the lock is cleared: The iOS/iPadOS setup assistant won’t proceed, and macOS won’t boot, except to recoveryOS.
Activation Lock and Supervised Devices
But this is all how Activation Lock works on unmanaged devices. But what about managed supervised devices in an organization? The biggest difference is that Activation Lock and Find My are no longer equivalent.
On supervised devices that an organization owns or controls, Activation Lock should be thought of completely separately from Find My, iCloud, or users’ Apple Accounts. On newly set up and enrolled supervised devices, Activation Lock is off by default in iOS, iPadOS, and macOS. Assuming your MDM solution isn’t overriding these defaults, on supervised devices that have just been set up, users can freely use iCloud and Find My without any risk of the device being locked to their individual Apple Accounts. This is by far the easiest way to manage Activation Lock for organizations: Don’t manage it at all.
Find My is a great way for end users to locate their devices, but it is not a good fit for admins wanting to track organizational lost or stolen devices. There are alternatives for locating those iOS and iPadOS devices with MDM Lost Mode. All device types can be locked or remotely erased as well. For many organizations, those abilities offer enough control, without Activation Lock.
For devices that are erased, as long as they were previously configured for Automated Device Enrollment, they can automatically re-enroll into MDM (we recommend turning off enrollment authentication for lost and stolen devices). And, in fact, automatic re-enrollment could prove to be even more useful than Activation Lock because the former can allow you to continue to gather information about the device, whereas Activation Lock will entirely block the ability to set up the device until cleared.
User vs Organization-linked Activation Lock
If you do want to take advantage of Activation Lock, MDM offers two ways to manage it: by allowing user-linked Activation Lock (essentially re-combining Find My and Activation Lock on managed devices), or, for iOS and iPadOS devices in Apple Business Manager, by directly turning it on without an Apple Account; for the purposes of this post, we’ll call the latter organization-linked Activation Lock.
For user-linked Activation Lock, MDM first requests an Activation Lock Bypass Code (sometimes abbreviated as “ALBC”) from the device; it then essentially tells the device, via an MDM settings command, that it’s okay to allow Activation Lock now. If an Apple Account was already signed in to iCloud with Find My turned on, this action then recombines Find My and Activation Lock and links that device to that user’s Apple Account. If no Apple Account is signed in, the next time one does sign in and turns on Find My, the device will be locked to that Apple Account.
For organization-linked Activation Lock for iOS and iPadOS devices in Apple Business Manager, MDM doesn’t have to interact with the device at all. Remember that the source of truth for Activation Lock is Apple’s servers.
With this method, after generating its own bypass code and associated lock data, (versus requesting it from the device, as with the user-linked workflow,) MDM sends an instruction to Apple’s servers to turn on Activation Lock for this device. If the request is successful, that device becomes Activation Locked on Apple’s servers, without being tied to an Apple Account of a user using the device (if there is one). Instead, it’s locked to the organization. Organization-linked Activation Lock was developed and released in iOS 9.3, when Apple introduced Shared iPad, so that organizations could still lock multi-user iPad devices to themselves rather than a specific user.
(Note: At present, when associating the device to the organization, Apple ties Activation Lock to the Managed Apple Account of the Device Manager in Apple Business Manager who created the MDM server token.)
Activation Lock Management in Apple Business Manager
In the summer of 2024, Apple added a longstanding feature request from organizations to Apple Business Manager: support for turning off Activation Lock for devices listed in an organization’s Apple Business Manager instance. This means that regardless of how Activation Lock got turned on for a device, it can easily be turned off as long as the device was in Apple Business Manager before the device was Activation Locked.
Turning off Activation Lock in Apple Business Manager requires your user role to have the Manage Device privileges. More information on Activation Lock Management in Apple Business Manager can be found in the Apple Business Manager User Guide.
Putting It All Together
So what does all of this mean for your deployments in practice? If you have no interest in managing Activation Lock, and if the other controls that MDM provides are sufficient to ensure device security, simply make sure your MDM solution isn’t changing the default behavior of ensuring that Activation Lock remains off on supervised devices.
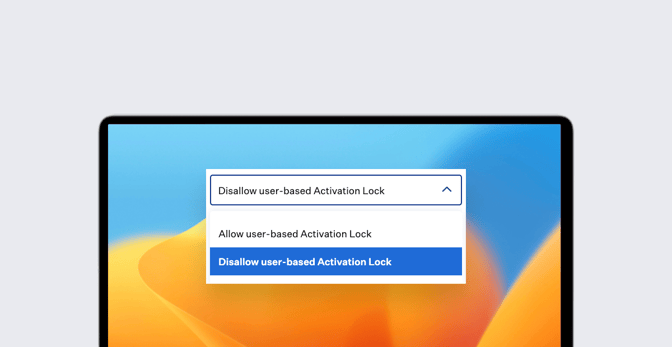
If you do want to allow user-linked Activation Lock, check the settings in your MDM solution for where this is configured, as well as where to find the bypass code you’d need to turn off Activation Lock if a user were to leave the organization before signing out of iCloud. (In Kandji, this is set in the Automated Device Enrollment Library Item; the bypass code can be found in the device actions menu on a specific device. Explicitly allowing Activation Lock for Mac computers enrolled using downloaded enrollment profiles is not supported.)
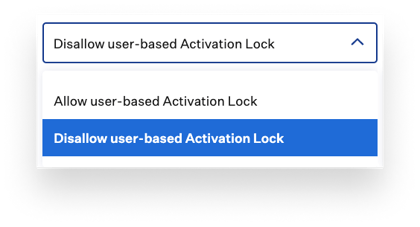 For organization-linked Activation Lock, check the settings in your MDM solution for where this is configured, as well as where to find the bypass code you’d need to turn off Activation Lock on the device. Note that some solutions do not display a bypass code for this method of Activation Lock and instead only have the option to turn it off directly with Apple. (In Kandji, this is set in the Automated Device Enrollment Library Item in the iPad and iPhone sections; the MDM-generated bypass code is visible and can be found in the device actions menu on a specific device.)
For organization-linked Activation Lock, check the settings in your MDM solution for where this is configured, as well as where to find the bypass code you’d need to turn off Activation Lock on the device. Note that some solutions do not display a bypass code for this method of Activation Lock and instead only have the option to turn it off directly with Apple. (In Kandji, this is set in the Automated Device Enrollment Library Item in the iPad and iPhone sections; the MDM-generated bypass code is visible and can be found in the device actions menu on a specific device.)
Check with your MDM solution to see if it supports turning off Activation Lock directly with Apple; sometimes this can happen as a part of erasing a device, for example. Alternatively, a bypass code can always be entered in the Apple Account password field during setup on iOS or iPad OS devices, or can be entered in recoveryOS on Mac computers by choosing Recovery Assistant > Activate with MDM Key in the menu bar.
For devices in your organization’s Apple Business Manager instance, you can also turn off Activation Lock there during a device reset, which may often be the easiest option.
Managing Activation Lock: Additional Tips and Tricks
There are a few gotchas to be aware of when it comes to managing Activation Lock in an organizational setting:
- If you do choose to use Activation Lock of either type, communicating to staff and community members when appropriate that your devices are secured in this way is generally a good practice and maximizes the effectiveness of the theft deterrence aspect. This is especially true for dense deployments of iPad which can become known across a community.
- As of the writing of this post, on a device that is Activation Locked and prompting for an Apple Account, you’ll be able to tell if it’s organization-linked Activation Lock if both the username and domain suffix are obfuscated. With user-linked Activation Lock, the domain remains visible and only the username is obfuscated.
- For organization-linked Activation Lock on iOS and iPadOS, you can also enter the Managed Apple Account credentials for the account that generated the MDM server token in Apple Business Manager at the Activation Lock screen. This is often just a last resort, especially now that organization-linked Activation Lock can be turned off using Apple Business Manager for devices that are listed there.
- Only one type of Activation Lock can be active at a time. If both user-linked and organization-linked are attempted, the first lock will always win.
- For user-linked Activation Lock, the bypass code that MDM requests from the device isn’t available for continuous retrieval in perpetuity. It is only available during the first 14 days after the request is originally made. This is especially important to consider for migrations from one MDM to another, as a device that was allowed to turn on Activation Lock in MDM A won’t be automatically unlocked simply by enrolling into MDM B, and the bypass code won’t be available to MDM B either. Apple Platform Deployment stresses the importance of keeping a copy of previous bypass codes when doing an MDM migration, and this is why. While still important to ensure you have access to Activation Lock bypass codes, some of the risk is mitigated now that Activation Lock can be turned off using Apple Business Manager for devices that are listed there.
- Mac computers that are enrolled into MDM using device enrollment (by installing a downloaded enrollment profile) automatically become supervised at that time. This is a huge difference between Mac and iOS/iPadOS devices. This means it’s possible for a previously unmanaged Mac to enroll into MDM and become supervised for the first time, at the point of enrollment. Because it had never been supervised before, it can provide a bypass code to MDM when requested. But because the computer was unmanaged before enrollment, if a user was signed into iCloud and had Find My turned on, Activation Lock would still be on. The bypass code provided to MDM would not turn it off; it would be valid only for the next time the device is Activation Locked. For that reason, when enrolling Mac computers that have never been managed before into MDM, it’s vital to add a step to the enrollment process requiring users to turn off Find My Mac before enrolling. One small exception to this is if the device was available in Apple Business Manager but not enrolled into MDM at the time Find My Mac was turned on; Activation Lock would then be able to be turned off in Apple Business Manager.
- For organizations, AppleCare Enterprise Support can sometimes assist with turning off Activation Lock when it’s possible to provide original proof of purchase for the device(s). That process is heavily gated and limited in the number of unlocks they’ll assist with in a given span of time. It should be relied on only as an absolute last resort, and hopefully, is needed far less often now that Activation Lock can be turned off for eligible devices in Apple Business Manager.
You get the greatest control over Activation Lock when MDM is in place and the device is supervised from the very beginning of its lifecycle. This means you should use Apple Business Manager and Automated Device Enrollment whenever possible, and thoroughly check the settings configured in your MDM solution for how Activation Lock will be managed (or not).
With thorough and proper planning, Activation Lock can either be a useful theft deterrent feature for your organization’s devices, which you can easily turn off if needed, or it can be something you simply don’t think about at all. It’s entirely up to you.
About Kandji
Kandji is the Apple device management and security platform that empowers secure and productive global work. With Kandji, Apple devices transform themselves into enterprise-ready endpoints, with all the right apps, settings, and security systems in place. Through advanced automation and thoughtful experiences, we’re bringing much-needed harmony to the way IT, InfoSec, and Apple device users work today and tomorrow.