Guide for Apple IT: Endpoint Detection and Response (EDR)
 Kandji Team
Kandji Team
Mac malware has been around as long as the Mac itself. But historically, the problem received little attention from Apple and its customers. That neglect was largely benign because, while Mac malware did exist, it remained relatively rare. The examples that did proliferate tended not to carry the same risks as their Windows counterparts; more often, they were proofs of concept rather than genuine dangers.
But as the Mac gained popularity over time—especially in the enterprise—the need for malware protection grew. Apple itself joined the fight in 2012 with the formal release of Gatekeeper and the requirement that apps distributed through the App Store be sandboxed. It has steadily expanded Mac’s arsenal since then.
Many third-party antimalware technologies that have come to market for the Mac have focused on the consumer market. But there’s also a significant market for enterprise-ready solutions. Many of those solutions fall into a sector Gartner dubbed Endpoint Detection and Response (EDR). (Kandji has recently introduced an EDR solution of its own.) Here are the essentials about EDR that anyone who works with the Mac in the enterprise should know.
What Is Endpoint Detection and Response (EDR)?
Let’s start with the ten-second definition: Endpoint Detection and Response (EDR) is a technology that monitors endpoints, such as laptops, desktops, and servers, for security threats. (While iOS and iPadOS have been targeted by security threats, we’re focusing on threats and solutions built for macOS.)
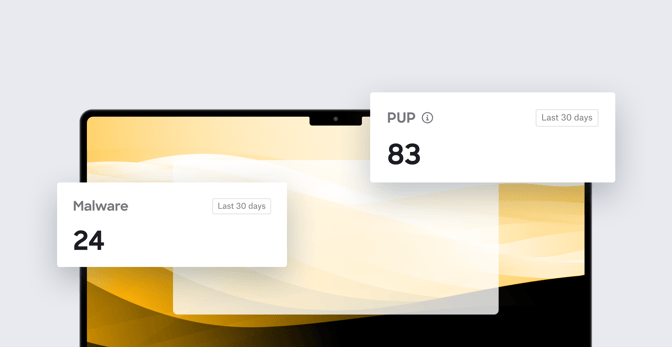
Those threats can come in many shapes, including malware and potentially unwanted programs (PUPs), which an EDR solution can detect. When it detects such a threat, it can respond in several ways.
That’s the short version. Now let’s break that down a bit more.
What Kinds of Threats Can EDR Detect?
As we’ve said, EDR solutions look for many types of threats, which can be classified into two broad categories: malware and potentially unwanted programs (PUPs).
Malware
Malware can take a variety of forms. They include viruses, trojans, adware, spyware, and ransomware. They can infect Mac computers through several vectors, including malicious websites (which may download unwanted files to your Mac), email attachments, fake software updates, and social engineering tactics. Once installed, Mac malware can steal sensitive data, encrypt files, hijack the system, or spy on user activities.
For individual users, Mac malware can compromise their privacy by stealing personal information, such as login credentials, credit card details, and browsing history. Ransomware can take over computers, encrypting files and then demanding payment to decrypt them. Malware can also create backdoors in the system, allowing attackers to remotely control devices to access organization resources, send spam, or launch distributed denial-of-service (DDoS) attacks.
For organizations, malware can disrupt business operations and cause downtime, data loss, and reputational damage. It can also lead to compliance violations, financial losses, and legal liabilities. Malware can also spread laterally within the organization’s digital infrastructure, infecting other endpoints and potentially compromising systems and data.
PUPs
PUPs are software programs that, while not explicitly malicious, may have unwanted or harmful effects on computers and their users. They can include browser extensions, adware, toolbars, system optimizers, and other software that users might unwittingly (or even wittingly) download and install without understanding the consequences. One notable but often overlooked type of PUP: Games. If end-users are surreptitiously playing them on Mac computers they use for work, that could be a security risk.
On users’ computers, PUPs might excessively consume system resources or display annoying pop-ups and ads. They may also change browser settings, obfuscate rogue VPN connections, redirect users to malicious websites, or track their online activities.
Within organizations, PUPs can compromise the security and integrity of the corporate network, exposing sensitive data and systems. Like malware, they may also violate compliance regulations, leading to legal and financial problems. While they might not be malicious themselves, they may compromise system security, leaving gaps that malicious actors could exploit.
How Does EDR Work?
Different EDR solutions take different approaches to detecting malware and PUPs.
Endpoint Threat Detection with EDR
The most common approach is to look at file hashes (or other signatures). (Hashing mathematically generates a unique numeric string based on a file’s attributes.) EDR solutions can examine the hashes (or other signatures) of files on the computer and compare them against databases of known malicious files. If they detect a known malicious file, they can respond.
Apple-specific EDR solutions can also take advantage of Apple’s Endpoint Security framework (ESF), which (in Apple’s words) “is a C API for monitoring system events for potentially malicious activity.” It gives security solutions real-time visibility into potentially malicious activity, such as executing processes or mounting file systems, without requiring access to the macOS kernel.
Many solutions also do process-monitoring or behavior-based analysis, which is to say they monitor processes or behaviors on the endpoint that could indicate malicious intent. That means tracking how files are being used and which users and processes are using them.
Often, these approaches are combined. So, for example, if a file’s hash identifies it as potentially malicious, its processes may then be monitored for potentially dangerous activity.
Some EDR solutions use sandboxing or cloud-based analysis to check files. The first means isolating suspicious files or processes in a controlled environment where their behavior can be observed. The latter involves uploading suspicious files to a cloud-based platform for further analysis.
Many signs that EDR solutions look for come from threat intelligence feeds, which stay up-to-date on the latest threats and attack techniques. EDR vendors might also have threat researchers on staff to look for new threats that haven’t been discovered or publicized. They may utilize machine learning algorithms to look for patterns and trends in file behavior that may indicate malicious activity, even if the file is not already known to be a threat.
When protecting against malicious files, an EDR solution might monitor them before they execute, after, or both. Pre-execution monitoring means examining files, typically for known signatures before they are executed. Post-execution monitoring looks at files after they start running; the EDR solution then looks for suspicious file activity, network connections, and system events.
Incident Response with EDR
The “response” part of EDR is relatively straightforward, compared to the detection piece. Solutions have a few ways to respond when the detection engine spots something suspicious.
Kill processes: If the EDR detects that a piece of malware or a PUP has started up, it can kill that process, so it doesn't continue to run.
Quarantine files: This means moving the malware file or files to a different location from which they can’t run. In Kandji EDR, for example, we use Apple Archive to lock the file, with an encryption key unique to each device and in a directory location that only the Kandji Agent and the system itself can access.
Alerts/notifications: The EDR solution needs to let admins know when they’ve detected something malicious (or just suspicious). These notifications may take many routes, from email to (in Kandji’s case) Slack. Some solutions also offer APIs, through which customers can create their own notification workflows.
Allow/block lists: Finally, many EDR solutions let admins create specific lists of files that are allowed to run, even if the solution’s detection rules flag them as suspicious, as well as block lists that bar specific files regardless.
How Do EDR Tools Work With Other Security Technologies?
Ideally, Apple-focused EDR solutions work in conjunction with Apple Platform Security. That security framework includes several interlocking tools that are purpose-built to protect Mac computers.
Gatekeeper: Gatekeeper helps protect against malicious software by blocking untrusted apps from running on the Mac. It uses a combination of code signing and verification to ensure that only trusted apps can run on the system.
XProtect: XProtect offers protection against known malware. It uses a signature-based approach to detect and block known malicious files, including Trojans, worms, and other types of malware.
FileVault: FileVault provides full-disk encryption for macOS to secure data at rest. It encrypts all data on the Mac's hard drive, including the operating system and user data, to protect against unauthorized access.
System Integrity Protection (SIP): SIP helps prevent unauthorized changes to the macOS operating system. It restricts access to critical system files and directories, preventing malicious software from modifying system files and components.
Each of these features addresses part of the malware problem. EDR solutions provide an extra layer of security on top of what Apple built into the Mac.
EDR vs. Antivirus
Many organizations have already deployed antivirus software on their endpoints. EDR and antivirus apps do overlap somewhat in their functionality, but there are significant differences.
Scope: Antivirus software typically focuses on detecting and preventing malware, including viruses, Trojans, and other types of malicious software. EDR solutions, on the other hand, provide more comprehensive endpoint protection, including detection and response to more advanced threats such as zero-day exploits and fileless malware.
Detection: Antivirus software typically uses signature-based detection, scanning and comparing files and other data against a database of known malware signatures. EDR solutions, as we’ve noted previously, may use a broader range of real-time detection techniques.
Response: Antivirus software typically has limited response capabilities, often only quarantining or deleting infected files. EDR solutions are generally more flexible in responding to a detection event and will generally provide more insight and information on the threat identified.
The need for Mac security is still often overlooked or underestimated by users and admins. But the Mac itself isn’t overlooked or underestimated by bad actors. This means that, as an Apple admin managing a fleet of devices, you need a scalable, enterprise-ready security solution. And EDR is a critical component of that solution.
About Kandji
Kandji is the Apple device management and security platform that empowers secure and productive global work. With Kandji, Apple devices transform themselves into enterprise-ready endpoints, with all the right apps, settings, and security systems in place. Through advanced automation and thoughtful experiences, we’re bringing much-needed harmony to the way IT, InfoSec, and Apple device users work today and tomorrow.