How Integrating EDR with MDM Boosts Mac Endpoint Security
 Kandji Team
Kandji Team
We’ve talked before about why endpoint detection and response matters and about how important it is for you, as an Apple admin, to have a security solution in place for the devices you manage. You know that the threat landscape—especially for Mac—has changed and that the old complacency about Apple security is no longer viable.
But what are you actually doing—or going to do—about all that? One strategy you need to consider: Use a solution that integrates device management (MDM) solution with endpoint detection and response (EDR).
We explored that idea recently in a panel discussion with three Kandji customers who have implemented our Endpoint Detection & Response for Mac: David Patrick (director of security and compliance at Neural Payments), Mario LaPorte (IT manager at TensorIoT), and Ryan Donnon (director of IT at First Round Capital). We also invited renowned Apple security expert Patrick Wardle, founder of the Objective-See Foundation, to provide his perspective.
Deploying Mac Security Settings and Tools
As Patrick Wardle explained, MDM has long been used to push out security settings to endpoints. Using a device management solution, admins can ensure that the security features built into macOS are turned on and configured correctly.
So, for example, MDM solutions can help you configure Gatekeeper on Mac endpoints, make sure FileVault is turned on, specify the kinds of passwords users create, and much more.
But MDM can do more than just enforce security settings: It can also be used to deploy security software to endpoints, just as you do with other apps. It can help by providing the entitlements that security apps need to do their work: access to the disk, the right to read files, and so on.
Without MDM, those apps would have to bother users to get those permissions. Those users would have to spend time and attention clicking on popups, answering prompts, providing passwords, and so on. Automatically providing the entitlements that security apps need via MDM means less is required of users—and (as we’ve said before) making things easy for users is critical to the success of any security program.
“If you're negating or detracting from the user experience,” Wardle pointed out, “that security tool is not going to last very long.”
Apple’s security framework also makes deploying security tools easier for admins, who don’t need to fiddle as much with the tooling. And it’s easier for the developers of those tools, who don’t need to build a lot of user interactions into their software.
In fact, when the conversation turned to the idea of deploying security tools without MDM, Ryan Donnon said, “I would almost say it's impossible—especially now, post-Covid when distributed workforces are so common. It could be done. But it would be brutal.”
EDR and MDM Integration
According to our panelists, MDM can help with security in a third way—if it’s integrated with EDR in a single unified solution (as it is in Kandji). All three have deployed Kandji’s MDM-plus-EDR solution in their organizations.
As David Patrick told us, “The more I looked into different deployment methodologies, and what it would require to manage standalone solutions, the resources it would consume on our team, the advantages of a security solution integrated with MDM became clearly evident.”
And that’s how it played out. The integration is so seamless that, when his team did the initial pilot installation of Kandji EDR, “Most of the users didn't even know it had happened.”
Mario La Porte’s experience was similar. When deploying Kandji EDR, his team formed a small test panel with some of his company’s developers. He messaged those testers that he was going to remove the old EDR solution and install a new one. “I sent that to eight initial users, and they said, ‘Okay, cool.’ About an hour later, I got messages from three or four of them: ‘Hey, when is this going to finish?’ And I said, ‘It's been done for about an hour.’”
When that test run was complete, he took the results to his leadership team. Because they already knew Kandji, the sell was relatively easy. Once he got their approval, he spent about a week documenting the new system and explaining to his teams why the company was moving away from their previous EDR solution. Once that communication process was done, he says it took maybe 30 minutes to roll out the new EDR to the rest of the organization.
“Users don't see anything on their end. There’s no user intervention that needs to happen. They don't have to click a thousand different things—allowing different network proxies or SSL certificates. It just works. “
Since the initial roll-out, he’s particularly appreciated the integration between MDM and EDR when it comes to onboarding new users. “When we get a new employee and they initially get that laptop, we know it’ll have all the features we want, it'll adhere to our security policies and protocols, and they’re protected with EDR.”
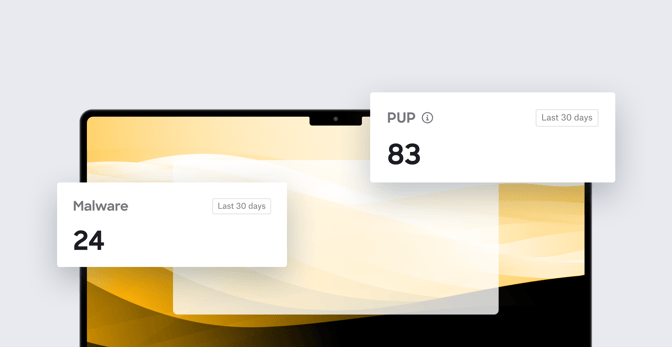
Ryan Donnon’s story echoed those same themes. His team trialed the new EDR solution in observation mode (so it wasn’t quarantining suspicious files) in parallel with their existing EDR application. “It saw some things that our previous EDR didn't catch—luckily, just adware that isn't necessarily malicious, but no one wants.”
With that successful trial in hand, he went to company execs for the green light. “I get a lot of leeway from my leadership team to implement what I recommend. So when I said that there's this new tool that’s going to be just as good if not better than the EDR we're using, plus implementation is going to be easier, it's going to be on every machine always, and there won’t be issues with Mac updates—all those things bucketed together made it a super easy sell.”
Once he had the leadership team’s approval, the rollout was fast. “The fact that it's just two clicks of a button in the MDM you’re already using just made a world of difference. People didn't really notice anything.”
To see the entire discussion, head over to our MDM + EDR event page.
About Kandji
Kandji is the Apple device management and security platform that empowers secure and productive global work. With Kandji, Apple devices transform themselves into enterprise-ready endpoints with all the right apps, settings, and security systems in place. Through advanced automation and thoughtful experiences, we’re bringing much-needed harmony to how IT, InfoSec, and Apple device users work today and tomorrow.